The goal of Malware Attribute Enumeration and Characterization (MAEC™), pronounced “mike,” is to provide a basis for transforming malware research and response. By eliminating the ambiguity and inaccuracy that currently exists in malware descriptions and reducing reliance on signatures, MAEC aims to transform malware research and response by improving communication, reducing potential duplication of malware analysis efforts, and allowing for faster development of countermeasures by enabling the ability to leverage responses to previously observed malware instances.
MAEC is a standardized language for sharing structured information about malware. The MAEC data model can be represented as a connected graph of nodes and edges where MAEC top level objects define the nodes and MAEC relationships define the edges. A relationship is a link between MAEC objects that describes how the objects are related.
As shown in the diagram, MAEC defines several top-level objects: Behaviors, Malware Actions, Malware Families, Malware Instances, and Collections. Relationships between objects (including Structured Threat Information Expression (STIX™) cyber observable objects) are depicted by directed edges in the diagram: embedded relationships (those that are specified directly on a top-level object as an object property) are labeled in black font (labels correspond to the property names), and direct relationships are labeled using a blue background (labels correspond to literal values for the relationship type).
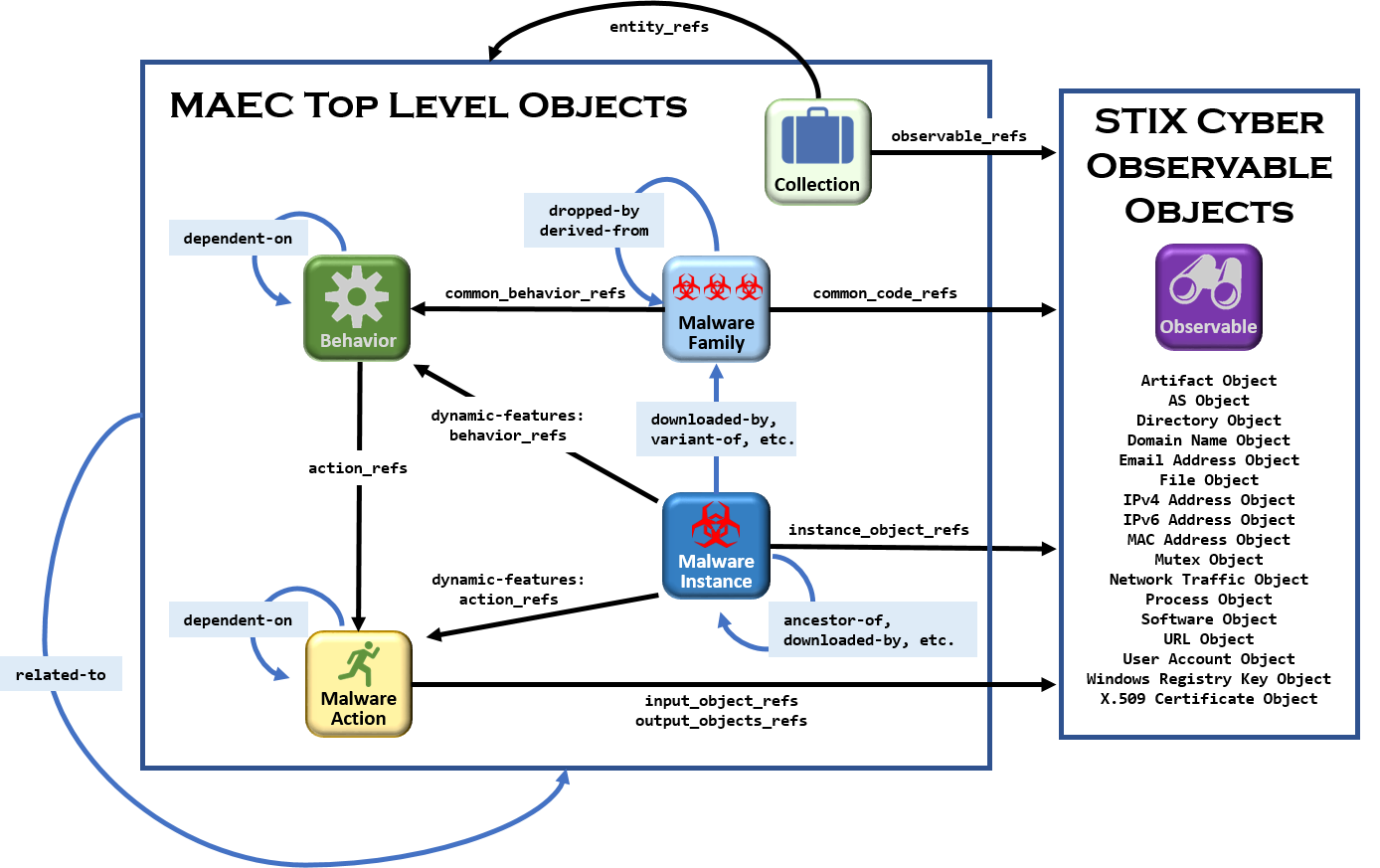
See the MAEC Core Specification for detailed information about top-level objects and direct and embedded relationships.
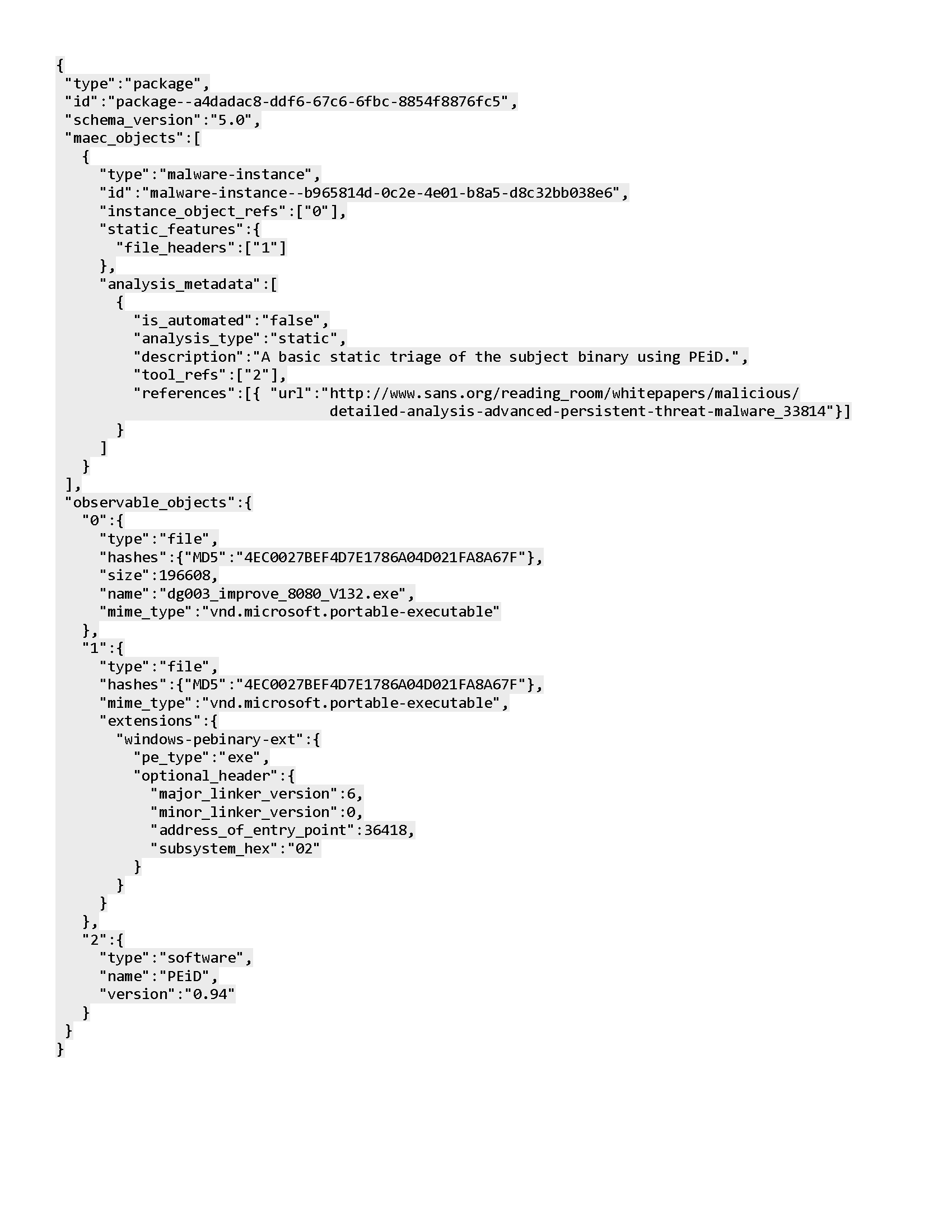
The example MAEC Package shown below captures results of static analysis performed with the PEiD tool on a malware instance.
Even without a formal understanding of the MAEC data model, it should be clear that the information captured includes the entry point and subsystem defined in the PE headers of the file, as well as the version of the linker used in linking the code.
NOTE: Additional examples are given in the MAEC Core Specification and on the Use Cases page.